[networking]
protocols = ["BGP", "OSPF", "IS-IS", "ECMP", "TCP/IP", "DNS", "DHCP"]
switching = ["VLANs", "802.1Q", "STP/RSTP", "LACP", "ACLs"]
tools = ["Wireshark", "Scapy", "tcpdump", "Mininet", "SNMP", "NetFlow"]
[programmable_dataplane]
language = "P4_16"
targets = ["BMv2 simple_switch", "Intel Tofino (TNA)"]
concepts = ["match-action tables", "header parsing", "stateful counters", "CMS sketches"]
[sdn]
controllers = ["P4Runtime", "Ryu", "OpenFlow"]
switching = ["Open vSwitch", "BMv2"]
[scripting]
primary = ["Python", "Bash"]
familiar = ["PowerShell", "JavaScript", "SQL", "Perl"]
infra = ["Git", "GitHub Actions", "Docker", "Ansible", "REST APIs"]
[security]
siem = ["Splunk (SPL)", "Microsoft Sentinel (KQL)"]
edr = ["CrowdStrike", "Microsoft Defender"]
vuln_mgmt = ["Nessus", "Qualys", "Nmap"]
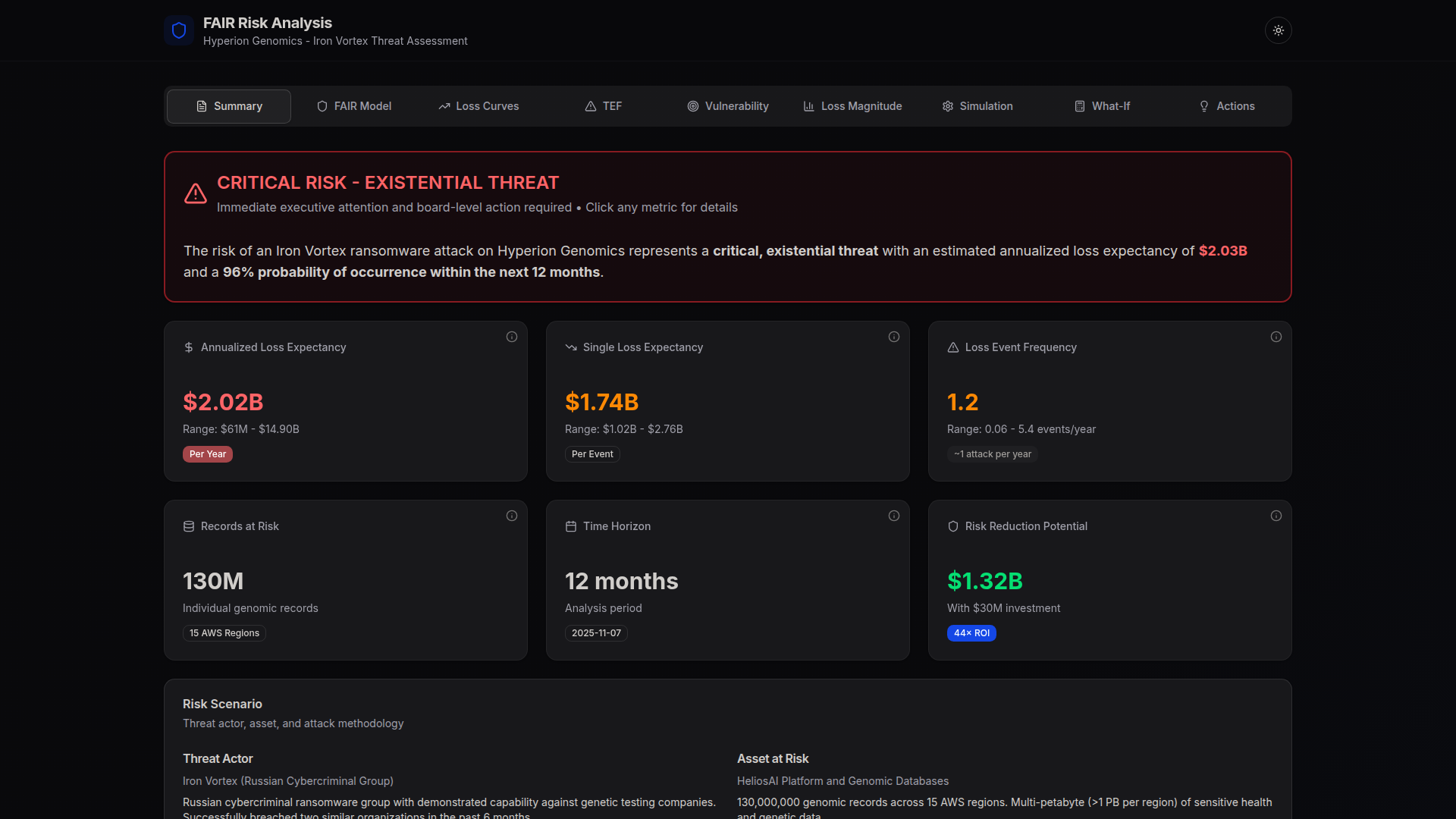
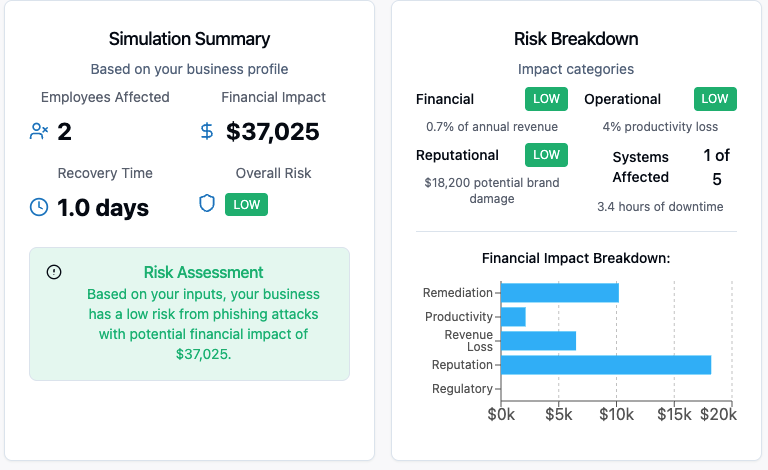
frameworks = ["NIST CSF", "NIST 800-53", "ISO 27001", "HIPAA", "FAIR", "MITRE ATT&CK"]
[ml]
focus = "traffic classification, anomaly detection"
tools = ["scikit-learn", "pandas", "numpy"]
[systems]
os = "Linux (Ubuntu, daily driver)"
server = "Windows Server"
cloud = "Microsoft Azure"